
We upgraded our email infrastructure with a secure Mail Gateway, stronger filtering, spam and virus protection, 14-day quarantine, and a new enterprise-grade em…
How we handle business email, why we introduced stricter protection mechanisms, and what this means for Network Technology clients.
Business email is no longer just a mailbox. It is one of the most critical access points to business operations, clients, contracts, invoices, and internal communication.
That is why we performed a significant upgrade of our email infrastructure to achieve a higher level of security, reliability, and ease of use.
These improvements are part of our ongoing implementation of best practices and security standards, aligned with upcoming ISO 27001 certification and GDPR compliance requirements.
Network Technology is part of an international company, which allows us to apply proven practices and high standards in network and information security. All measures are focused on protecting communication, data, and business processes.
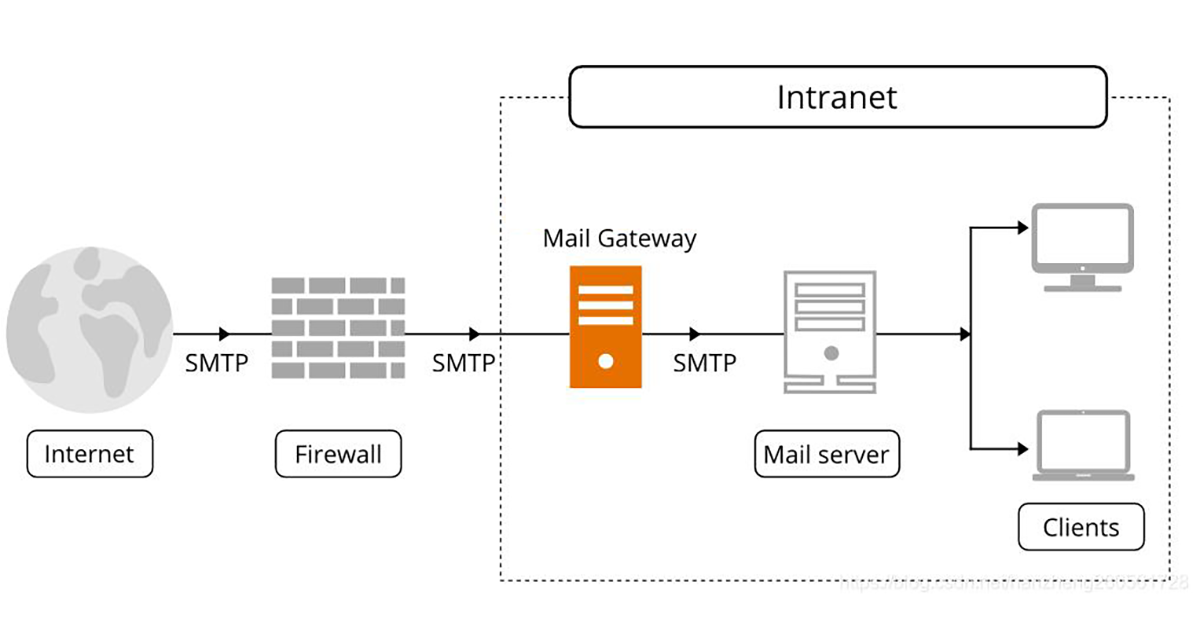
All incoming and outgoing emails now pass through a secure Mail Gateway. This acts as an intermediate protection layer that analyzes email traffic before it reaches the mailbox or is sent externally.
These mechanisms operate in real time and have one main goal, to protect clients from data loss, unauthorized access, malicious files, and account compromise.
If you are expecting an email that has not arrived, we can check its status. Quarantined messages are stored for 14 days, during which they can be reviewed and released if necessary.
In cases of repeated unwanted or malicious sending behavior, IP addresses may be added to our protection system and restricted. Access can be restored after additional verification if needed.
In the near future, minimum password security requirements will be enforced. Passwords shorter than 8 characters will not be allowed.
The new requirements will include:
This is not meant to complicate usage, but to protect email accounts. Weak passwords are often the fastest path to compromised accounts, data leaks, and abuse of business communication.
In addition to the Mail Gateway, we now offer a next-generation email service aimed at larger corporate clients with higher requirements for security, control, and functionality.
Standard hosting email is usually limited to basic functionality.
Enterprise email introduces control, policies, security, tracking, user management, and higher reliability.
Unlike mass cloud solutions like Office 365, this system is under our control. This allows a higher level of customization, flexibility, and adaptation to specific organizational needs.
It is important to note that the Mail Gateway protection is active for all clients, ensuring a consistently high level of security for every mailbox.
The system supports distribution lists, groups of email addresses combined under a single address.
For example:
Sending to one address automatically delivers the message to all members of the group. This simplifies communication and reduces the risk of missing recipients.
Email is one of the most commonly attacked services in any organization. It is used for phishing, malware delivery, fake invoices, password theft, and social engineering attacks.
That is why email security must be treated as part of the overall security strategy, not as a standalone configuration.
The goal of these changes is simple, more secure and more reliable email communication.
Everything is done to protect communication, data, and business continuity.
We do not treat email as a simple service that just needs to "work". For us, it is part of the entire IT environment.
When there is an email issue, we do not check only Outlook. We analyze DNS, SPF, DKIM, DMARC, domain reputation, server status, logs, filters, access control, and traffic behavior.
That is the difference between a basic email setup and a professionally managed email infrastructure.
If you have questions, are missing an email, or need additional setup for your team, we can assist with analysis, configuration, and ongoing support.
Contact us and we will review your setup and provide a clear and practical solution.